PHISHING & SCAMS
By Michael Cochran, Director of IT, Website Administration, California Advocates Management Services
While email safety has always been a concern, with the advent of ransomware, spear phishing, spoofing, more people working remote and other current security events, it has become a very active attack vector for those wanting to take advantage. With many scams today, if it doesn’t start with a phone call/text message, it probably starts with an email.
Most of us have probably witnessed the usual attempts, such as scammers targeting employees by spoofing a CEO or manager’s identity. They typically want money wired or gift cards purchased. We often think ‘I would never fall for that!’, but it happens repeatedly. This is because they don’t always come up when you might be expecting them. In fact, some pick their targets and those they are impersonating very carefully. They will even pick a time when they know the target is off guard and/or under pressure. This is known as “spear phishing”, rather than a general ‘phishing’ attempt where they throw out a broader net trying to get anyone to bite. When spear phishing is combined with social engineering, spoofing, etc., it can be a very effective method.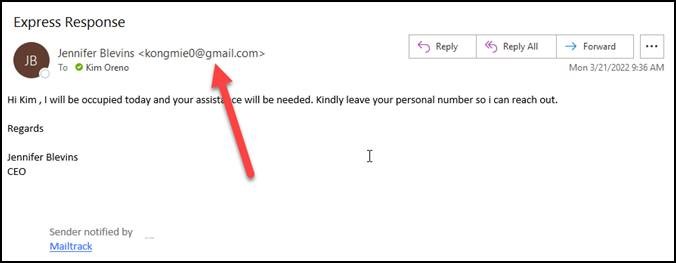
You can often check if an email is ‘spoofed’ by looking at the email address it was sent from. Many times they will just spoof the name and not the email address itself. However, they can do that as well. So, the best way is to look at the details of an email through the settings of your email client to see whom it came from. Specifically, look for the email header in the properties of the email in question.
Targeted scams typically focus on a group of users with something that group is interested in. One of the examples we see often, is someone purporting to be selling a contact list of members of a specific organization as either sales leads or simply contact lists. For most people, they wouldn’t know it was a scam unless they purchased the list. However, this is a known scam. The best way to prevent yourself from falling prey to this scam, is to always verify the contact before purchase.
An example like the above came up recently. The email purported to be from a female named Megan Fox (I think most of us have heard that name before) from a domain that sounded like it might be an actual sales lead provider. It was targeting someone that might be interested in such a list.
We found that the domain was owned by a male in India belonging to a different organization in India. Also, further investigation showed the domain did not load a website. This also showed that the domain was registered just months before. Was this a sales leads scam? this a phishing attempt or worse, a spear phishing attempt? Was this someone that simply scrubbed the available public information and is now trying to sell it? It is hard to say, as the target didn’t take the bait. Instead, they forwarded it to someone that might know or might want to know about this list and the fact that it was out there.
Some good articles and resources to help to ensure safe email handling and what to look for in the most typical phishing attempts and/or scam emails are linked below. But remember, email isn’t the only attack vector for this. Phone calls, text messages and even the old school faxes and snail mail are used.
If you are not 100% sure, check, check, and triple check. May I also suggest that if you have an IT resource, use and abuse it. If they are bothered by such inquiries, hire a good one…no one wants to deal with the “Company Computer Guy”.
USEFUL RESOURCES:
https://www.securitymetrics.com/blog/top-10-types-phishing-emails
https://www.securitymetrics.com/blog/7-ways-recognize-phishing-email
https://consumer.ftc.gov/features/scam-alerts
https://consumer.ftc.gov/articles/how-recognize-and-avoid-phishing-scams



0 Comments